When it comes to securing a building, it's not about just throwing up a few cameras or installing better locks. Real security is about creating smart, overlapping layers of protection. You need to think like a potential threat and build a defense that combines physical barriers, modern technology, and well-trained personnel to protect your property from the outside in. This is the blueprint for shifting your security posture from reactive to proactive.
Your Blueprint for Total Building Security
As a property manager, facilities director, or HOA board member, your primary responsibility is maintaining a safe and secure environment. It only takes one security incident to cause a major financial loss, but the damage to your reputation and the loss of tenant confidence can be far worse.
The biggest challenge is often knowing where to start. Effective security isn't just one product you buy off the shelf; it's a complete system, thoughtfully planned and executed by a trusted partner.

The ultimate goal here is to create a resilient environment where no single point of failure can compromise your entire property. This guide goes beyond the basics to give you a practical framework for making the right decisions.
The Four Pillars of Building Security
Before diving into specifics, it's crucial to understand the fundamental components of any solid security strategy. In our 26 years of experience, we've seen that the most secure properties are the ones that successfully integrate these four pillars.
| Security Pillar | Objective | Examples |
|---|---|---|
| Deterrence | Discourage potential threats before an attempt is even made. | Visible security officers, marked patrol vehicles, clear signage, and bright lighting. |
| Detection | Identify unauthorized activity the moment it happens. | Motion sensors, door/window contacts, glass-break detectors, and surveillance cameras. |
| Delay | Slow down an intruder to create a window for your response team to act. | High-quality locks, reinforced doors, security window film, and physical barriers like fences. |
| Response | Intervene and manage an incident swiftly and effectively. | On-site security patrols, 24/7 remote monitoring, and established emergency protocols. |
Think of it this way: a camera system (Detection) is far more effective when you have a professional security officer (Response) ready to act on what that camera sees.
A successful security plan ensures these pillars work in concert. When one layer is bypassed, another is already in place to stop a breach.
This multi-layered approach is all about building a defense-in-depth strategy tailored to the unique risks your property faces, whether it's a commercial high-rise in San Jose or a sprawling residential community in Los Angeles.
Conducting a Meaningful Security Risk Assessment
Before you can secure a building, you have to know exactly what you’re protecting—and what you're protecting it from. A professional security risk assessment is much more than a simple checklist. It’s a deep dive into your property’s daily rhythm, its unique layout, and its specific weak spots. This process is the bedrock of any effective security plan.

The goal is to move past assumptions and use real-world analysis to make smart, cost-effective decisions. Instead of just reacting to incidents after they happen, you start to anticipate and prevent them.
Identifying Your Critical Assets
First, you have to pinpoint what needs the most protection. Assets aren't just physical items; they include people, sensitive information, and the operational continuity of your business.
For a property manager, that list often looks like this:
- People: Every person on site, from tenants and employees to visitors and contractors.
- Property: The building itself, common areas, critical HVAC systems, and individual tenant spaces.
- Information: Tenant records, access control data logs, and any proprietary company information stored on-site.
- Reputation: The standing of your property in the community is a significant asset that directly impacts occupancy rates and property value.
When you truly understand your most critical assets, you can prioritize your security efforts and put your budget where it will have the greatest impact. It ensures you're not just securing doors but protecting the entire ecosystem of your property.
Analyzing Threats and Pinpointing Vulnerabilities
Once your assets are clearly defined, the next step is to analyze potential threats and find the physical or procedural weaknesses—the vulnerabilities—that an intruder could exploit. This requires a trained eye and the ability to think like an adversary.
A poorly lit parking garage isn't just a dark space; it's an opportunity for vehicle break-ins. An unmonitored side entrance isn't just convenient for staff; it's an unmanaged access point.
This is where partnering with an experienced security provider makes a significant difference. With over 26 years of experience, our hands-on leadership team can spot risks that an untrained eye would easily miss. We walk your property, observe the flow of people, physically test access points, and review existing protocols to find these gaps.
We document all findings to create a clear, actionable roadmap. This roadmap then directly shapes your security strategy, right down to the development of comprehensive and effective security guard post orders that give officers clear directives. A thorough assessment ensures your security measures are tailored to solve real-world problems, creating a genuinely safer environment for everyone.
Mastering Perimeter Control and Access Management
Your first line of defense isn't a camera or an alarm—it's your perimeter. This is where you establish a clear boundary, making it understood where your property begins and unauthorized entry is forbidden. A strong perimeter shuts down opportunistic threats long before they reach your doors.
Effective perimeter security is a smart mix of physical and psychological deterrents. Think of it this way:
- Physical Barriers: Fences, gates, and bollards are the obvious workhorses. But don't forget your windows. For some real-world perspective, look into the benefits of hurricane impact glass, which is engineered to resist severe impacts from both storms and break-in attempts.
- Strategic Landscaping: You don't need to build a fortress. Simply planting dense, thorny bushes under first-floor windows can make access far more difficult and unappealing.
- Territorial Reinforcement: This is the subtle element that makes a huge difference. Clean grounds, clear signage, and bright, well-placed lighting all send a powerful message: this property is managed, monitored, and not an easy target.
Implementing Smart Access Control
Once you’ve solidified your perimeter, the next layer is controlling who gets through it. This is the job of access control, and it's all about making sure only the right people get into the right areas. There's no one-size-fits-all solution; a Class A office building has completely different needs than a construction site in San Jose.
A high-end office tower might opt for a frictionless system using mobile credentials, letting tenants breeze through with just their smartphones. This is often paired with a visitor management platform that logs guests, prints temporary badges, and notifies the host when their visitor arrives.
In contrast, a construction site's priorities are durability and strict oversight. This usually means rugged key card readers at a single entry point, manned by a dedicated security officer who personally verifies every contractor and logs every vehicle.
The bottom line: technology is a tool. The most sophisticated access control system is only effective when managed by well-trained people who can respond to alerts and ensure protocols are followed consistently.
The Role of Intrusion Detection
Beyond managing who should be there, you need a way to detect who shouldn't. This is where your alarm and intrusion detection systems come into play. This graphic breaks down the simple but crucial workflow for handling a potential breach.
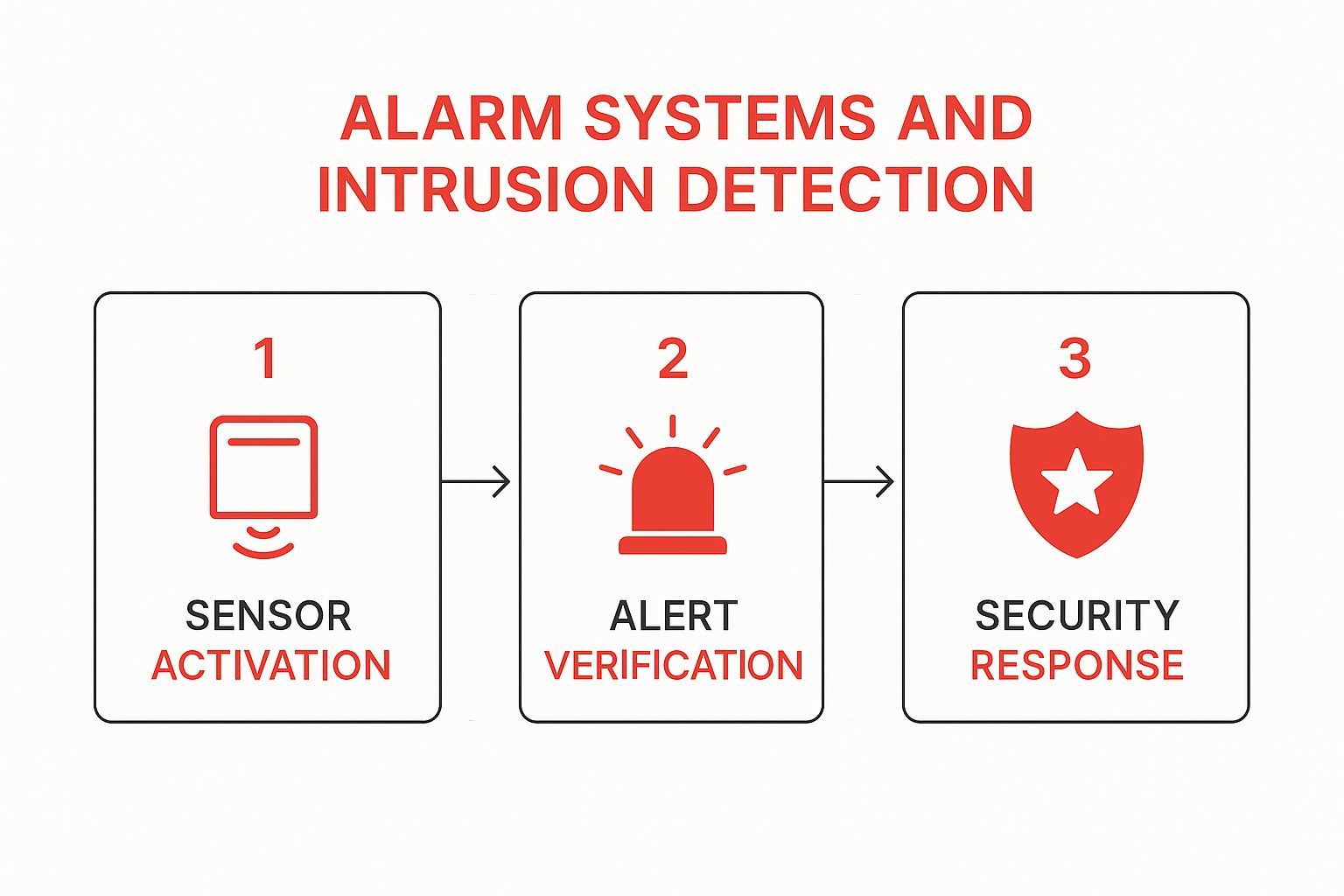
This process shows why you need both technology and human verification. It’s the key to reducing false alarms and ensuring a fast, appropriate response when a real threat is detected.
It's also worth remembering that the hardware and software making these systems possible are part of a much larger supply chain. These days, supply chain vulnerabilities are a primary risk for building security. In fact, a staggering 54% of large organizations now see these challenges as a major obstacle to their cyber resilience. Why? Because one compromised supplier can open the door to widespread problems.
Weaving Surveillance and On-Site Patrols into One Cohesive System

True security isn’t just about having cameras; it’s about making your technology and human expertise work together as a single, intelligent unit. A camera can record a crime, but a professional security officer can often prevent it from happening in the first place. That synergy transforms your property’s protection from a passive recording system into an active, breathing shield.
Just installing cameras and hoping for the best often creates a false sense of security. The true power is unlocked when that eye in the sky is directly connected to a responsive presence on the ground. This blended approach ensures that the moment a camera flags an issue, an immediate and intelligent human response is already in motion.
Moving Beyond Passive Recording to Active Surveillance
Too many properties are stuck with cameras that do little more than provide footage to review after a break-in. This is reactive security. Active surveillance, on the other hand, turns your cameras into a proactive detection network, all managed through a 24/7 Security Operations Center (SOC).
Think of the SOC as the nerve center for your entire security apparatus. When an alert comes in—say, motion is detected near a restricted loading dock after hours—it doesn't just ping an automated notification. Instead, trained professionals instantly pull up the live feed, verify the threat, dispatch a patrol officer, and coordinate with law enforcement if the situation warrants it.
This approach closes the critical gap between detection and response. It means a potential threat at a loading dock in Los Angeles or a parking garage in San Francisco is met with immediate human intervention, not just a digital recording for someone to look at the next morning.
This level of active oversight is more crucial than ever. Today's security infrastructure is a web of interconnected digital systems, which opens up new avenues for attack. In fact, by mid-2024, vulnerability-based cyberattacks had already surged by 124% compared to the previous year. You can dig into more cybersecurity statistics and insights to see just how important this integrated vigilance has become.
Strategic Camera Placement for Maximum Impact
Effective camera placement is a game of angles and priorities. It's about covering your most vulnerable areas with crystal-clear lines of sight, not just blanketing the property in a sea of cameras.
Here are the key areas we always prioritize:
- Entry and Exit Points: Every primary door, loading dock, and pedestrian gate needs to be covered. You need to know who is coming and going at all times.
- Parking Lots and Garages: These are high-risk zones. Well-placed cameras are a massive deterrent for vehicle break-ins and can capture critical details like license plates.
- Common Areas: Lobbies, mailrooms, and amenity spaces are prime targets for unauthorized access and package theft.
- Perimeter Fences: The goal is to detect a potential intruder before they ever reach the building itself. Monitoring the property line is your first line of defense.
The Power of a Visible and Accountable Presence
While technology provides the eyes, a professional security patrol provides the visible presence that makes potential criminals think twice. The simple sight of a marked patrol vehicle or a uniformed officer making their rounds sends a powerful message: this property is protected. It's often the single most effective deterrent against opportunistic crime.
At Overton Security, we blend human expertise with smart technology to ensure total accountability. Our officers utilize a GPS-enabled guard tour system, requiring them to scan checkpoints and file detailed digital reports—complete with photos—in real-time. This gives property managers a transparent, verifiable record of every patrol, offering complete peace of mind. It’s this combination of a visible deterrent and documented accountability that truly secures a building in today's world.
Building a Culture of Security with Strong Policies
High-tech cameras and reinforced doors are excellent tools, but they’re only half the story. The most advanced security system in the world can be defeated by simple human error or a lack of awareness. Real, lasting security only happens when everyone—from your employees to your tenants and visitors—understands they have a part to play.
That’s where a strong security culture comes in. It’s about shifting the mindset from relying solely on hardware to creating a shared sense of responsibility for keeping the property safe. This culture is built on one thing: clear, practical, and consistently reinforced policies.
Developing Clear and Enforceable Protocols
A security policy shouldn't be a dusty binder on a shelf. It needs to be a living document that shapes how people act every day. The key is to make it simple enough for anyone to grasp and practical enough for them to follow.
For property managers and business owners, this means mapping out clear protocols for common situations:
- Visitor Management: How do guests sign in? Is a visible badge required? Who’s responsible for ensuring they don’t wander into restricted areas?
- Incident Reporting: What should someone do if they see a suspicious person or a broken lock? A straightforward process encourages people to report things immediately.
- Emergency Response: When a fire alarm sounds or a medical emergency happens, who is in charge? Where are the evacuation routes? Drilled, unambiguous procedures prevent panic and save lives.
These policies should be part of new employee onboarding and included in every tenant’s welcome packet. When the rules are clear, people naturally become active partners in the security plan.
The Critical Role of Trained and Consistent Personnel
Let's be honest, the security industry has a reputation for high turnover. This "burn and churn" approach creates a significant vulnerability. A security officer who just started last week doesn't know your building’s quirks, the faces of your long-term tenants, or the specific risks you face.
Investing in a security partner that focuses on officer retention and ongoing training is one of the smartest security decisions you can make. A consistent, professional officer becomes part of your team—a familiar face who builds trust and knows your property inside and out.
A well-trained officer does more than just watch a monitor; they engage with people, de-escalate potential conflicts, and respond to incidents with practiced confidence. They are the ones on the ground enforcing your policies and providing the immediate response that technology alone can't offer. If you're wondering what to look for, our guide on hiring the right security agency breaks it down.
As our buildings get smarter and more connected, this human oversight becomes even more critical. Global spending on cybersecurity is projected to hit a staggering $212 billion by 2025, largely because our physical infrastructure is now so deeply intertwined with digital systems. This trend underscores a modern reality: securing a building demands both a strong physical presence and sharp cyber awareness. You can dive deeper into these emerging cybersecurity trends to see what’s on the horizon.
Ultimately, building a great security culture is about reinforcing the simple idea that safety is a team sport. When you combine clear policies with dedicated, professional personnel, you create an environment where security isn't just a department—it’s woven into the fabric of your building's daily life.
Common Questions About Securing Your Property
After talking through the core strategies for securing a building, it's natural for a few practical questions to arise. With over two decades of experience, we've heard just about every question from property managers, HOA boards, and business owners across California. Here are some of the most common ones we get, with straightforward answers from our team.
How Often Should We Review Our Building Security Plan?
Think of your security plan as a living document, not something you write once and file away. It needs to evolve as your property does.
As a rule of thumb, we recommend a full, comprehensive review at least annually. But you should also revisit it anytime there's a major change—a new anchor tenant moves in, you complete a big renovation, or you notice a shift in neighborhood crime patterns.
And if an incident does happen? A post-incident review isn't optional; it's essential. This is your chance to find any weak spots in your protocol and strengthen them immediately. A good security partner will help you stay ahead of the curve, adapting your plan proactively instead of just reacting after the fact.
Is Visible or Discreet Security Better?
This is a classic question, but the answer isn't one or the other. The most effective security posture almost always involves a smart blend of both. You're creating layers, and each style has its own unique strengths.
- Visible Security: Think uniformed officers and clearly marked patrol vehicles. This is your frontline deterrent. It sends a clear message and discourages opportunistic threats. We see this work wonders everywhere, from bustling Los Angeles retail centers to active construction sites in San Jose.
- Discreet Security: Sometimes, you need eyes on a situation without disrupting the environment. Plainclothes officers or cleverly placed cameras are perfect for monitoring activity quietly. This approach is critical in high-end residential communities or corporate headquarters where maintaining a certain atmosphere is just as important as security itself.
The right balance depends on your property's specific culture and risk profile, which a professional assessment can pinpoint.
What Is the Biggest Mistake in Building Security?
Hands down, the most common mistake we see is the "set it and forget it" mindset. A property manager invests in a system, hires a firm, and then doesn't re-evaluate it for years. Technology evolves, tenants change, and new risks emerge. A security plan that isn't regularly updated, tested, and re-evaluated is practically guaranteed to fail when you need it most.
The second biggest error? Choosing a security provider based solely on the lowest price tag. This approach almost always backfires with high officer turnover, inconsistent service, and guards who don't have genuine knowledge of your site—ultimately costing you more in losses and headaches down the road.
Investing in a quality partner who focuses on training, officer retention, and real accountability delivers far greater value and genuine peace of mind. If you want to understand what really separates a professional service from the rest, our guide on finding the best security guard services near me is a great place to start. Real security is an ongoing commitment, not a one-time purchase.
A truly secure property is the result of a strong partnership. At Overton Security, our 26 years of hands-on experience and low manager-to-client ratio mean you get the attention and consistency you deserve. We blend human expertise with smart technology to protect what matters most.
If you're ready to build a smarter, more resilient security plan, we’re here to help. Contact us today to schedule a comprehensive security assessment for your property.







