Have you ever wondered what separates a security guard who is simply present from one who is truly effective? The answer often lies in their post orders—the detailed instructions that serve as the operational playbook for protecting your property. Think of them as the blueprint for your entire security program, guiding every action from routine patrols to critical emergency responses.
A well-written set of post orders is the difference between a reactive security presence and a proactive, professional security strategy that safeguards your assets and people.
Why Post Orders Are Your Security Program's Blueprint

Many property managers and HOA boards treat post orders as a one-time formality—a document to be signed and filed away. This approach misses their essential role in defining what a successful security presence looks like for your unique property.
Without clear, customized instructions, security protocols are left to an officer's personal judgment or generic training. This is where inconsistencies and significant risks can emerge. Effective post orders are the operational heart of your security strategy, translating high-level goals into daily, actionable tasks.
The Dangers of Generic Instructions
Generic or outdated post orders create immediate vulnerabilities. When instructions are vague, inconsistent service is nearly guaranteed. One officer might conduct a thorough patrol of the parking garage, while the next misses critical checkpoints entirely, leaving your property exposed.
This lack of clarity can lead to very real risks:
- Security Gaps: An order to "patrol the premises" is not actionable. A detailed order specifies which doors to check, what to look for at the loading dock, and when to inspect the pool area after hours. Specificity closes these gaps.
- Increased Liability: In the event of an incident, post orders are among the first documents reviewed in a legal dispute. Vague or missing instructions can be interpreted as negligence, weakening your legal standing.
- Inconsistent Officer Performance: Without a clear standard, officer performance will vary. This can create a frustrating experience for tenants and residents, causing them to question the value of your security investment.
At Overton Security, we have seen firsthand how detailed post orders transform a security program. With 26 years of experience, we know that investing time upfront to create a robust operational plan is the single most important step in protecting a client's property effectively.
A Foundation for Accountability and Quality
Well-crafted post orders do more than just outline tasks; they create a solid framework for accountability. They establish a clear performance benchmark that both you and your security partner can reference to ensure consistent, high-quality service.
This is especially critical for companies that oversee multiple sites, like those offering comprehensive property management services. Standardizing post orders across a portfolio is key to delivering consistent protection.
The security services industry is projected to reach $49.1 billion in revenue in 2025, with over 112,000 businesses in the market. In such a crowded field, providers who demonstrate operational excellence through detailed, meticulous planning are the ones who truly stand out. You can learn more about the market landscape in this IBISWorld report.
Ultimately, your post orders are a direct reflection of your commitment to safety. By treating them as a living, breathing tool for risk management, you empower your security team, reduce your liability, and ensure you receive the high-quality protection you're paying for.
The Anatomy of a High-Quality Post Order Document
A truly effective post order document is much more than a simple checklist. It is a detailed operational playbook that provides officers with absolute clarity and gives property managers complete transparency. The goal is to systematically eliminate ambiguity so that every instruction is actionable and verifiable.
This is the difference between hoping for security and actively managing it.
In our experience, inconsistent service often stems from one root cause: vague directives. When an officer has to interpret a generic instruction like "patrol the property regularly," their actions will inevitably vary based on experience, diligence, or other factors. Specific, detailed post orders remove that guesswork and variability.
From Vague Directives to Actionable Instructions
Let’s examine the common but flawed instruction: "Patrol the property regularly." What does "regularly" mean? Which areas are most critical? This kind of fuzzy language creates significant security gaps.
Now, let's contrast that with an instruction built for accountability:
Example: "At 10:00 PM, patrol the east perimeter fence line, starting at the main gate. Scan NFC tag #7 at the service gate. Report any signs of tampering or unauthorized access via the GTMS app, including a time-stamped photo of the area."
This tells the officer precisely what to do, where to do it, when to do it, and how to report it. There is zero room for interpretation. This level of detail is the bedrock of consistent protection for any site, whether it's a bustling commercial high-rise in Los Angeles or a quiet residential community in San Jose.
Core Components Every Post Order Must Include
While every property is unique, a solid post order is always built on the same foundational framework. From our 26 years of experience, these components are non-negotiable for a document that works effectively in the real world.
-
Site-Specific Emergency Contacts: This needs to go beyond just "Call 911." It should list direct lines for the property manager, on-call maintenance, and other key stakeholders, with clear guidance on when to contact each person.
-
Clear Chain of Command: Who does the officer call first? The document must outline the operational chain of command, from the on-site officer to their field supervisor, and up to Overton’s 24/7 Security Operations Center (SOC). This ensures any incident is escalated quickly for immediate support.
-
Detailed Patrol Routes and Checkpoints: A property map with designated patrol routes is essential. We integrate these routes with technology, like NFC tags or QR codes, to obtain verifiable proof that critical areas—such as mechanical rooms, fire exits, and parking garages—are being checked exactly as required.
-
Specific Access Control Protocols: Your instructions must detail the procedures for every entry point. This includes handling visitors, verifying contractor credentials, managing after-hours deliveries, and documenting every entry and exit in a digital log.
-
Incident Reporting Procedures: Define precisely what constitutes an "incident" and provide step-by-step reporting instructions. This should specify what information to collect, who requires immediate notification, and how to document the event in the digital reporting system.
Putting this level of detail together takes an upfront investment of time, but it pays lasting dividends in operational excellence and peace of mind.
For a great starting point, you can look at our security patrol checklist template to see how these elements fit together in a practical format. This structured, hands-on approach is what separates professional security from a simple on-site presence, and it's a core part of the quality-first philosophy we've built at Overton Security.
Essential vs Advanced Post Order Components
Not every site needs the same level of complexity in its post orders. While some components are fundamental for any location, high-risk or specialized facilities require more advanced layers of instruction and protocol.
Below is a breakdown of what we consider "essential" for all sites versus "advanced" components reserved for properties with more complex security needs.
| Component | Essential (All Sites) | Advanced (Specialized Sites) |
|---|---|---|
| Emergency Procedures | Contact list (911, property manager), basic fire/evacuation plan. | Multi-stage escalation protocols, active shooter response, HAZMAT containment steps, specific medical emergency contacts. |
| Access Control | Visitor sign-in/out log, after-hours package handling. | Biometric scanner protocols, vehicle inspection procedures, multi-factor authentication for sensitive areas, contractor vetting. |
| Patrol & Surveillance | Designated routes, key checkpoint scans, visual inspection notes. | Covert surveillance guidelines, specific camera monitoring duties (e.g., watch Camera 5 from 2-4 AM), counter-surveillance sweeps. |
| Reporting | Daily activity log, standard incident report form. | Threat level assessment matrix, detailed use-of-force reporting, evidence handling/chain of custody procedures. |
| Technology Integration | Use of guard tour management app for reports and patrols. | Real-time SOC integration, drone surveillance protocols, license plate recognition (LPR) system alerts, alarm panel operation. |
This table helps illustrate how post orders can and should be scaled. The goal is always to provide the right level of detail for the specific risks and operational realities of the property being protected.
Adapting Post Orders for Your Unique Property
A generic set of post orders is a recipe for ineffective security. You simply can't treat a high-rise residential building in Los Angeles the same as a sprawling construction site in Fresno; their security challenges are worlds apart. To be effective, security instructions must be meticulously crafted for the specific environment, culture, and risk profile of your property.
This means moving beyond broad principles to drill down into the day-to-day operational realities of your site. The goal is to create post orders that feel as if they were written by someone who walks your property every day—because, ideally, they were developed in close collaboration with you. This partnership approach is what turns security officers into a seamless extension of your property management team.
Residential Communities: HOAs and Apartments
In any residential community, security officers are often the first and last people residents and their guests see. They must balance enforcement with genuine hospitality. The post orders must reflect this dual role, giving them clear guidance on how to keep the property safe while maintaining a welcoming atmosphere.
Vague instructions can lead to inconsistent enforcement, which is a fast way to frustrate an HOA board or property manager. Getting specific on directives for resident interaction, amenity control, and parking is key.
- Access Control: Lay out the exact protocol for verifying guests, contractors, and deliveries. Should officers call the resident for every guest, or is there a pre-approved list? How should they handle a high volume of food delivery drivers?
- Amenity Management: Be precise with opening and closing times for the pool, gym, and community rooms. Outline the steps an officer should take if residents are using amenities after hours, emphasizing a polite but firm approach.
- Parking Enforcement: The post orders need a clear map of resident, guest, and restricted parking areas. Instructions must specify the process for issuing warnings versus authorizing a tow and detail how to document every violation with photos.
Key Focus for Residential Post Orders: Protect people and property while enhancing the resident experience. All instructions should prioritize de-escalation, professional communication, and consistent, fair enforcement of community rules.
Commercial Office Buildings
For commercial properties, the focus shifts to tighter access control, tenant safety, and asset protection, usually on a much larger scale. Post orders must account for a high volume of daily traffic—employees, visitors, vendors—while keeping the perimeter secure, especially after business hours.
The document should serve as the operational playbook for the building's daily rhythm, including managing the morning rush, monitoring the loading dock, and executing the nightly lockdown. Crystal-clear instructions are essential for maintaining a professional and secure environment for every tenant.
- Visitor Management: Define the check-in process. Is pre-registration by the tenant required? What are the exact procedures for issuing and retrieving temporary access badges?
- After-Hours Protocols: Detail the lockdown sequence step-by-step. Specify which doors are secured, at what time lobby access switches to keycard-only, and how to conduct thorough floor-by-floor patrols to confirm all suites are secure.
- Emergency Response: Include specific instructions for fire alarms, medical emergencies, and power outages. This should include a list of key contacts from both property management and specific tenant companies.
Key Focus for Commercial Post Orders: Emphasize robust access control, professional tenant interaction, and meticulous after-hours security. The orders must protect both the physical property and the tenants' ability to conduct business without disruption.
Construction Sites
Construction sites present a unique set of vulnerabilities. They are packed with high-value materials and equipment but often lack permanent security infrastructure. Here, post orders are less about hospitality and all about deterrence and loss prevention. The mission is to prevent theft, vandalism, and unauthorized access that trigger costly delays and liability concerns.
Instructions must be direct and focused on securing the perimeter and controlling who and what comes and goes. Because these sites are constantly changing, post orders must be reviewed and updated frequently to adapt to each new phase of construction.
- Access Point Control: Restrict access to a single point of entry and exit for all workers and vehicles. Orders must require officers to log every person and vehicle, verifying their credentials and purpose on-site.
- Material and Equipment Protection: Identify and map the storage areas for high-value items like copper wiring, tools, and heavy machinery. Patrol routes must include specific, mandatory checks on these zones.
- Subcontractor and Visitor Escorts: To prevent individuals from wandering into sensitive areas, the rule should be firm: all non-badged personnel, such as inspectors or clients, must be escorted by an authorized representative at all times.
Key Focus for Construction Post Orders: The priorities are loss prevention and strict access control. Instructions must be unambiguous about securing assets, logging all site traffic, and identifying potential threats before they result in a loss.
Of course, even the best post orders are only as effective as the officers executing them. At Overton Security, we ensure our site-specific instructions are supported by comprehensive security officer training programs that prepare our team for the unique demands of any property. This commitment ensures the instructions you approve are brought to life by capable, prepared professionals.
Using Technology to Enhance Post Order Execution
Even the most well-written post orders are ineffective if they aren't followed consistently. In the past, property managers had to rely on paper logs and hope for the best. Today, that is no longer sufficient. The best security programs blend the experience of professional officers with the accountability that smart technology provides. This approach turns your post order binder into a living, transparent, and auditable operational tool.
This fusion of human expertise and technology isn't a luxury; it's the new standard for professional security. It gives property managers and HOA boards verifiable proof that every instruction is being carried out exactly as planned. The security services sector is growing for a reason—North America's security guard market has expanded by a remarkable 38% as businesses prioritize asset protection. This growth reflects a demand for more reliable and transparent security solutions.
Linking Instructions to Action with a GTMS
A modern Guard Tour Management System (GTMS) is the central nervous system of a tech-enabled security operation. At Overton Security, our officers use a GPS-enabled GTMS that ties directly into the post orders for each site. This is about more than just tracking an officer's location; it’s about verifying that specific actions are completed at critical points.
Here’s how it works on the ground:
- NFC Tags and QR Codes: We install small, durable NFC tags or QR codes at key checkpoints you want verified—such as the pool gate, a server room door, or a remote corner of the parking garage.
- Mandatory Scans: The post orders require the officer to scan these tags during their patrol. The GTMS logs the exact time and GPS location of every scan, giving you undeniable proof the officer was precisely where they needed to be.
- Task-Specific Prompts: When a tag is scanned, the GTMS can push a specific task from the post orders directly to the officer's device. For example: "Confirm rooftop access door is locked and bolted. Upload photo verification." This makes it virtually impossible for critical duties to be missed.
This simple process transforms a routine patrol into a series of verifiable, time-stamped events, providing you with complete peace of mind.
The diagram below shows how we tailor this process for different property types, turning your custom instructions into verified actions on the ground.
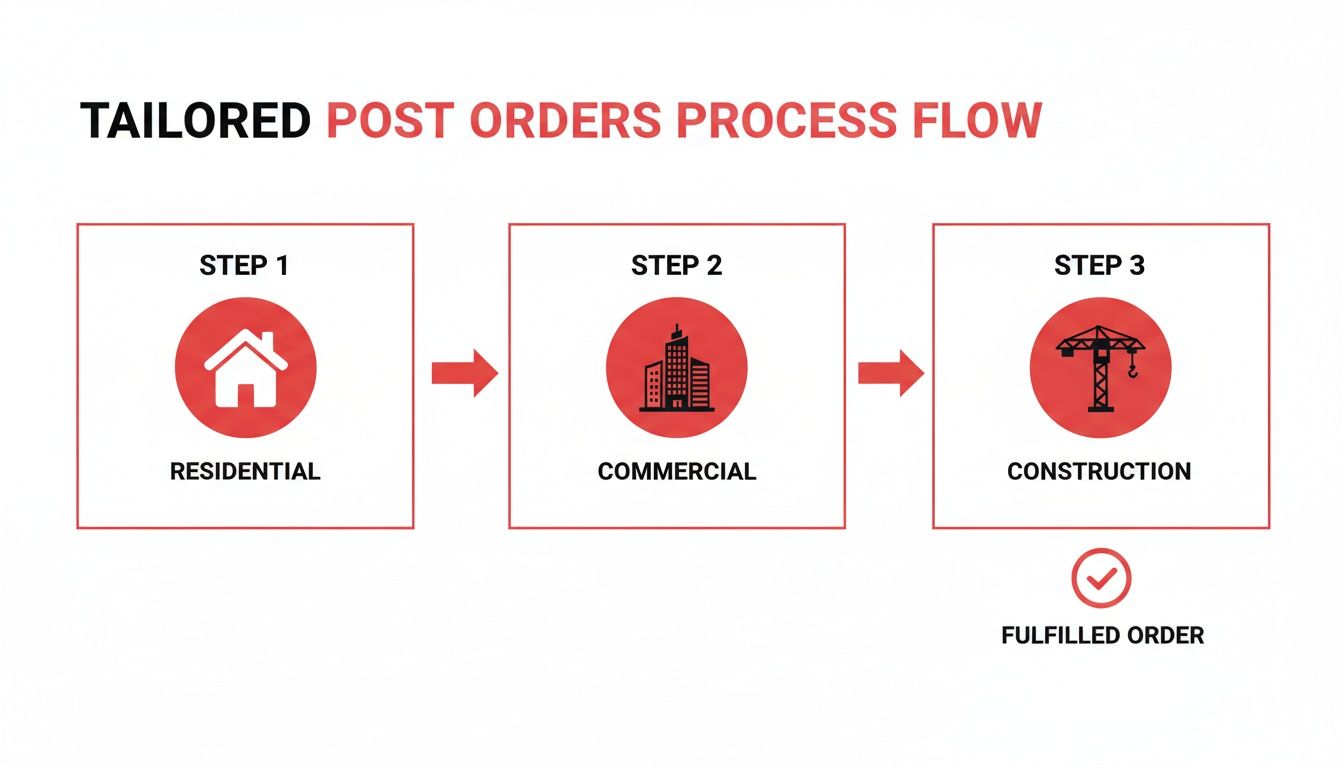
As you can see, while the core technology is the same, the specific checkpoints and tasks are completely customized to address the unique risks of residential, commercial, and construction environments.
The Power of Real-Time Digital Reporting
The days of deciphering illegible, handwritten reports submitted hours after an incident are over. Modern security technology allows our officers to document incidents the moment they occur, giving clients from San Diego to Sacramento immediate, verifiable information.
Digital reporting, built directly into the GTMS, enables officers to:
- Submit Incident Reports Instantly: Officers can file reports from their mobile device the second an issue is identified. No delays, no forgotten details.
- Include Multimedia Evidence: A picture is often worth a thousand words. Officers can attach time-stamped photos and videos to document a broken fence, an unauthorized vehicle, or a slip-and-fall hazard.
- Create Detailed Activity Logs: Every action, from a routine patrol check to responding to a tenant noise complaint, is logged in a clean, easy-to-read digital format.
In the same way that property maintenance management software brings efficiency to property operations, this level of tech integration brings accountability to security management. You’re not just hoping for compliance; you’re seeing it happen in real time. To learn more about how different systems can work together, see our guide on the integration of security systems and discover how a cohesive tech stack can make your entire site safer.
Keeping Your Post Orders Relevant and Effective

Crafting a detailed set of post orders is a critical first step, but it’s only the beginning. The long-term success of your security program hinges on what comes next: consistent training and proactive updates. A perfect document is of little use if it sits unread in a binder or if officers on the ground don't truly understand the strategy behind the instructions.
For a security plan to be effective, every officer needs to understand not just what to do, but why it's important for your specific property. This philosophy is at the core of our hands-on management approach at Overton Security and is backed by over 26 years of service.
Empowering Officers Through Effective Training
Onboarding a new security officer to your site should be more than a quick tour. It must be a structured training process built around the post orders. A field supervisor or account manager should walk the officer through every duty, explaining the context and potential consequences of each task.
This process turns abstract instructions into tangible, real-world actions and ensures the officer feels confident and prepared to represent your interests from their very first shift. This level of preparation is crucial. The investigation and security services industry employs 735,430 security guards, who make up 73.69% of the sector's total workforce. This large number highlights the vital role of well-trained security professionals. You can learn more with this statistical overview.
To ensure nothing is missed, a standardized training checklist is essential.
Site-Specific Officer Training Checklist
- Initial Document Review: Did the officer read the entire post order document and sign an acknowledgment form?
- Property Walk-Through: Were all patrol routes, designated checkpoints (including any NFC tags), and critical areas like utility rooms or fire panels physically pointed out?
- Access Control Drills: Has the officer role-played different access scenarios, such as visitor check-ins, contractor verification, and after-hours entry requests?
- Emergency Contact Protocol: Does the officer know exactly who to call—and in what order—for different types of incidents like medical emergencies, fires, or criminal activity?
- Technology & Reporting: Can the officer confidently use the Guard Tour Management System (GTMS), including scanning checkpoints and submitting digital incident reports with photos?
- Site-Specific Nuances: Have you thoroughly explained unique property rules, like HOA parking regulations or tenant-specific protocols in a commercial building?
A structured approach like this eliminates guesswork and establishes a clear performance standard from day one.
Establishing a Cadence for Review and Updates
Your property is not a static environment. Tenants change, construction projects evolve, and new vulnerabilities can appear. To remain an effective risk management tool, your post orders must evolve with your property. A "set it and forget it" mindset is a sure way to create security gaps.
A post order document should be a living blueprint for your security program. Regular reviews are not administrative tasks; they are proactive risk assessments that keep your protection strategy sharp and responsive.
How often you review your post orders should be dictated by the nature of your property. A stable, low-traffic site has different needs than a dynamic one with constant activity. We recommend a structured schedule to ensure your instructions never become outdated.
Recommended Post Order Review Schedule
A systematic review schedule ensures your security plan stays perfectly aligned with the day-to-day reality of your property. It’s a simple way to stay ahead of potential issues.
| Property Type | Recommended Review Frequency | Common Triggers for Immediate Update |
|---|---|---|
| Residential Communities | Annually | Change in HOA board or management, installation of new amenities (pool, gym), or a pattern of specific incidents (e.g., package theft). |
| Commercial Office Buildings | Semi-Annually | Arrival or departure of a major tenant, changes to building access systems, or significant renovations to common areas. |
| Construction Sites | Quarterly (or per phase) | Completion of a major construction phase (e.g., foundation to framing), significant changes in site layout, or high-value material delivery. |
| Retail Centers | Quarterly | Arrival of a new anchor store, seasonal changes in foot traffic (holiday season), or updates to loss prevention strategies. |
This commitment to proactive management is what separates an effective security partnership from others. By regularly revisiting and refining your post orders, you ensure your security program doesn't just look good on paper—it delivers real, measurable results where it matters most.
Your Top Questions About Post Orders Answered
Even with the best intentions, crafting and managing security post orders can bring up many questions. Over our 26 years in the field, we've heard from countless property managers, HOA boards, and business owners. Here are the answers to the questions that arise most often.
How Detailed Should My Post Orders Be?
A good rule of thumb is this: could an officer who has never set foot on your property before perform every duty perfectly, just by reading the post orders? If the answer is no, they aren't detailed enough. Any room for interpretation is room for error.
Effective post orders are specific, actionable, and verifiable. Instead of a vague instruction like, "Check all doors," a better version would be: "At the start of each shift, physically check and confirm all 14 exterior doors are locked. This must include the rear service entrance and the rooftop access hatch."
That level of detail ensures consistent service. It also reduces your liability by demonstrating that you’ve established clear, professional instructions. We always recommend including site maps, photos of key locations (like water shut-off valves or alarm panels), and a full contact list.
Who Is Responsible For Writing and Updating Post Orders?
The best post orders are always a collaborative effort between you and your security partner. As the property expert, you know your rules, operational nuances, and emergency contacts best. A professional security provider brings operational expertise, including best practices for patrols, incident response protocols, and legal considerations.
The most effective post orders are born from a partnership. The client provides the ‘what’ and ‘where,’ while the security provider delivers the ‘how’ and ‘why,’ ensuring the plan is both practical and professional.
Typically, the security company will draft the initial version after a thorough site assessment and consultation with you. However, you should always have the final review and approval. When on-site conditions change or a new risk emerges, the update process should be just as collaborative.
What Is The Legal Importance of Accurate Post Orders?
From a legal standpoint, accurate post orders are absolutely critical. In the event of an incident—such as a theft or an injury—your post orders serve as the official record of the duties assigned to the security team.
They can be presented in legal proceedings to demonstrate that both you and your provider acted with reasonable care. Conversely, vague or outdated post orders can become a significant liability, suggesting an inadequate security plan was in place. Think of them as a foundational document for both operational success and risk management.
How Do Post Orders Differ For An Armed Vs Unarmed Officer?
While core duties like patrol routes and reporting are often similar, the post orders for an armed officer must include crucial additional sections. The most important of these is a detailed Use of Force policy that is in strict alignment with state and local laws.
This section must leave zero room for interpretation. It needs to clearly outline the specific conditions under which force is authorized, mandatory de-escalation steps, and the exact protocols for reporting after any use-of-force incident. The orders will also cover strict rules for firearm storage, handling, and proof of regular qualification. This entire section of the document requires a thorough review by legal counsel to ensure all parties are protected.
Ready to build a security program based on clarity, accountability, and 26 years of experience? The team at Overton Security is here to help you craft post orders that protect your property and provide complete peace of mind.
Contact us today to schedule a comprehensive site assessment.